Three Products.
One Binary.
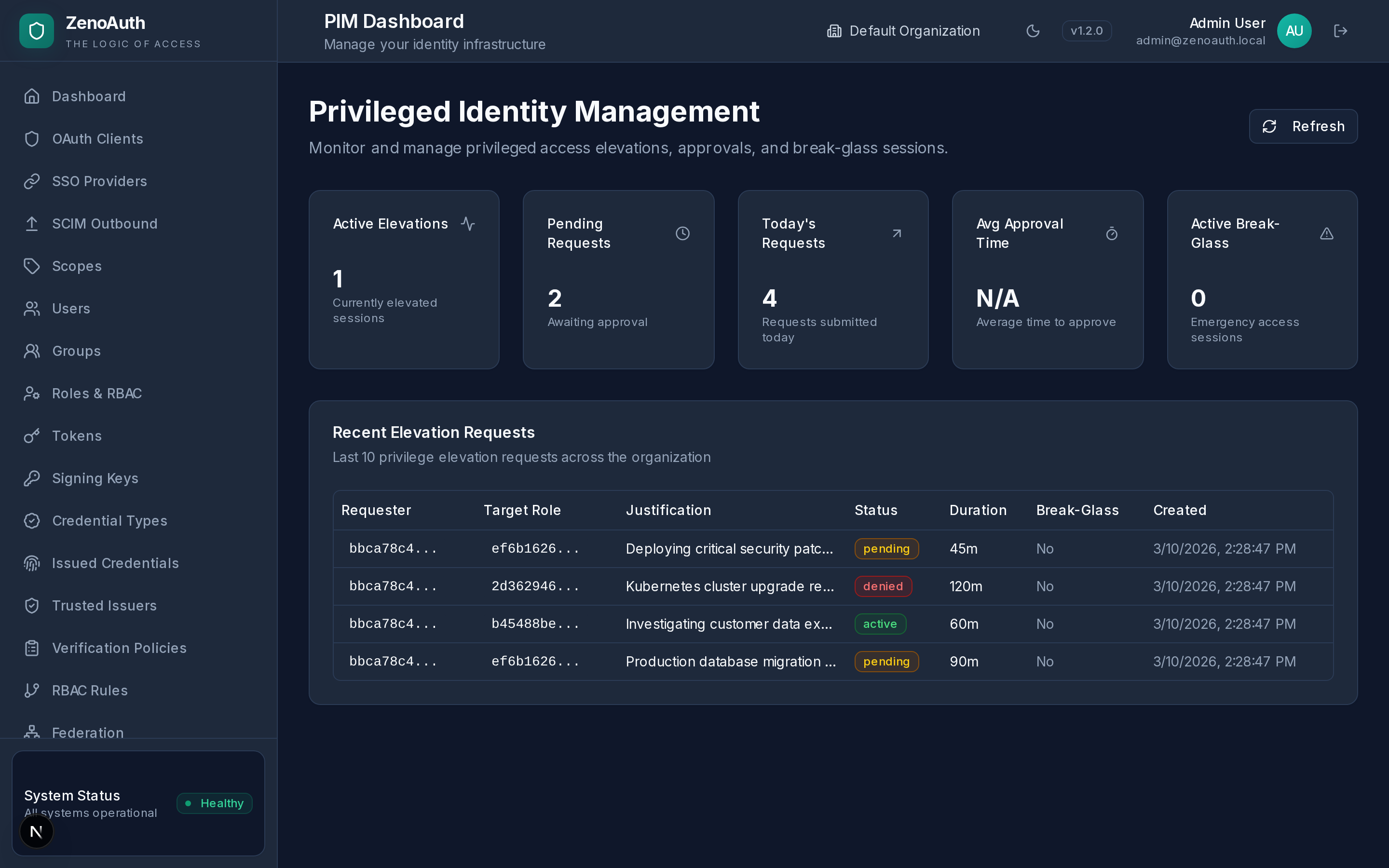
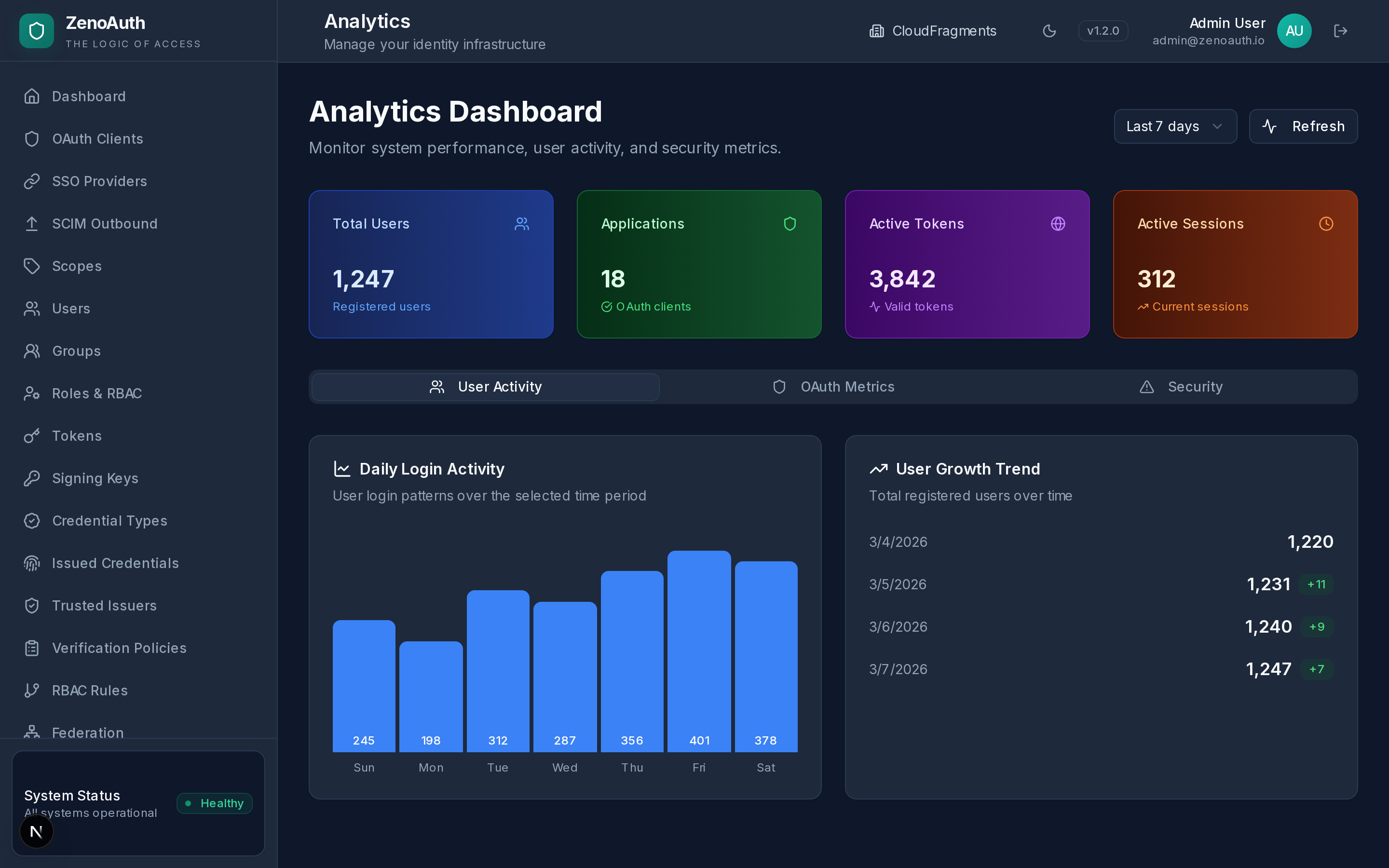
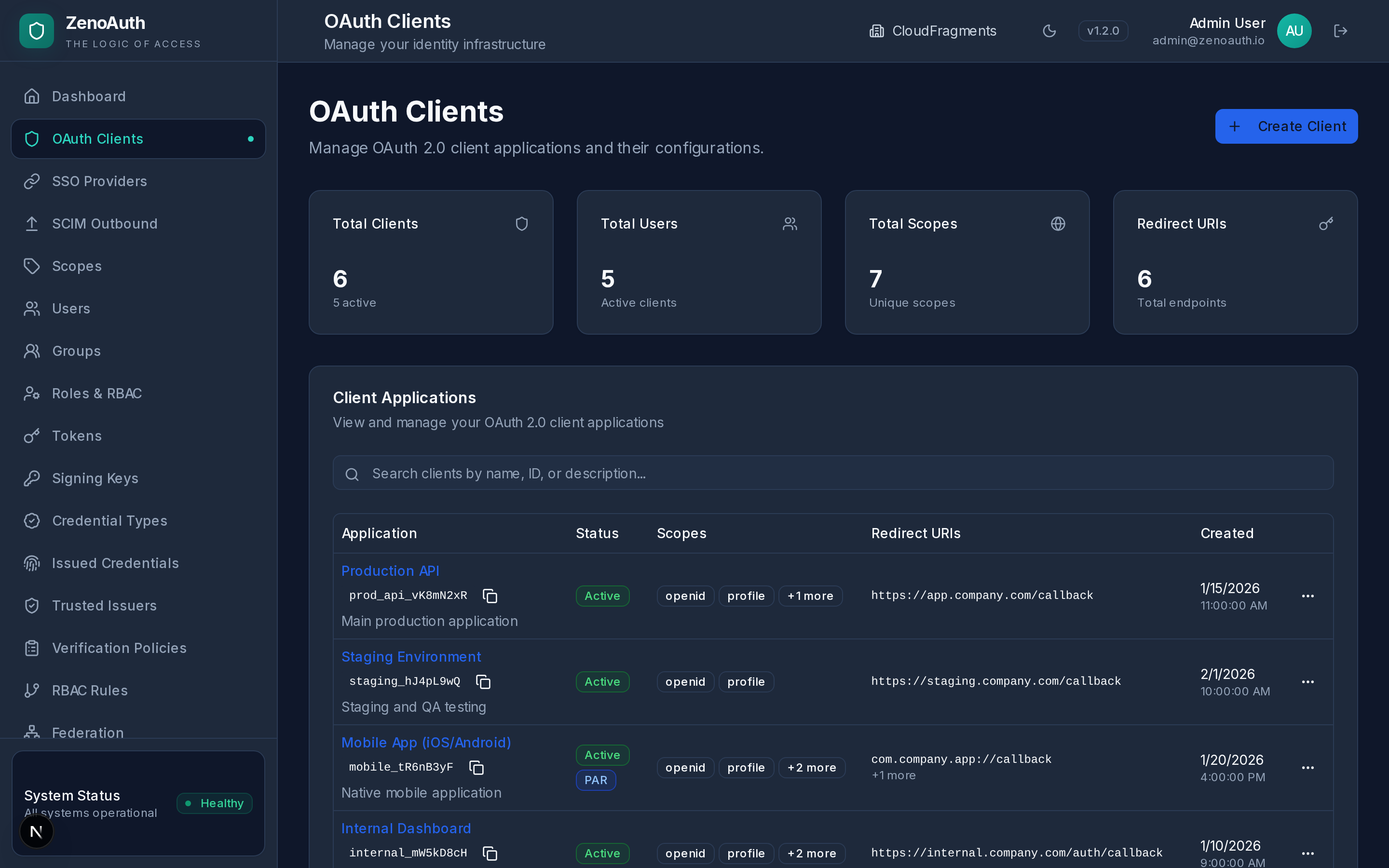
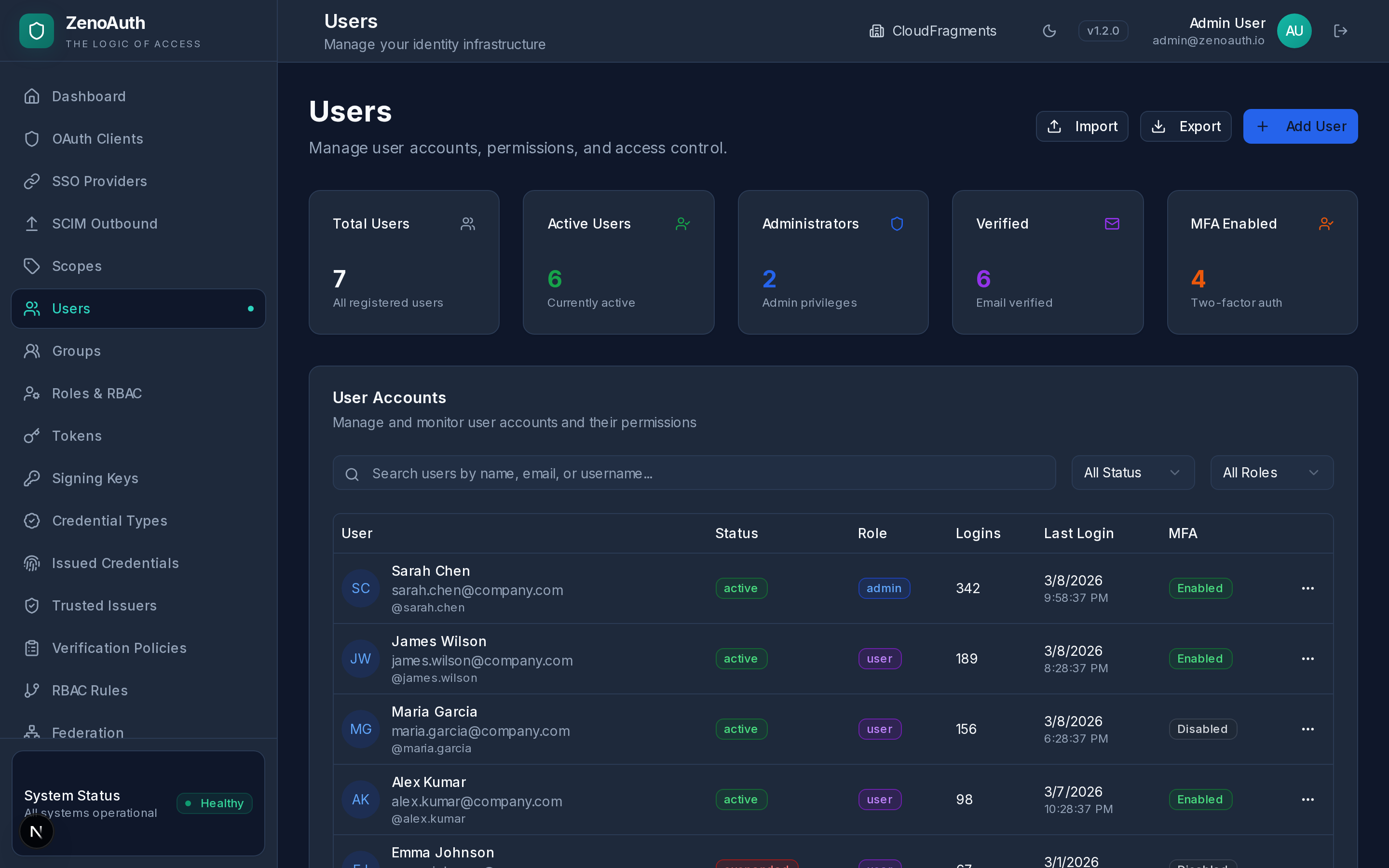
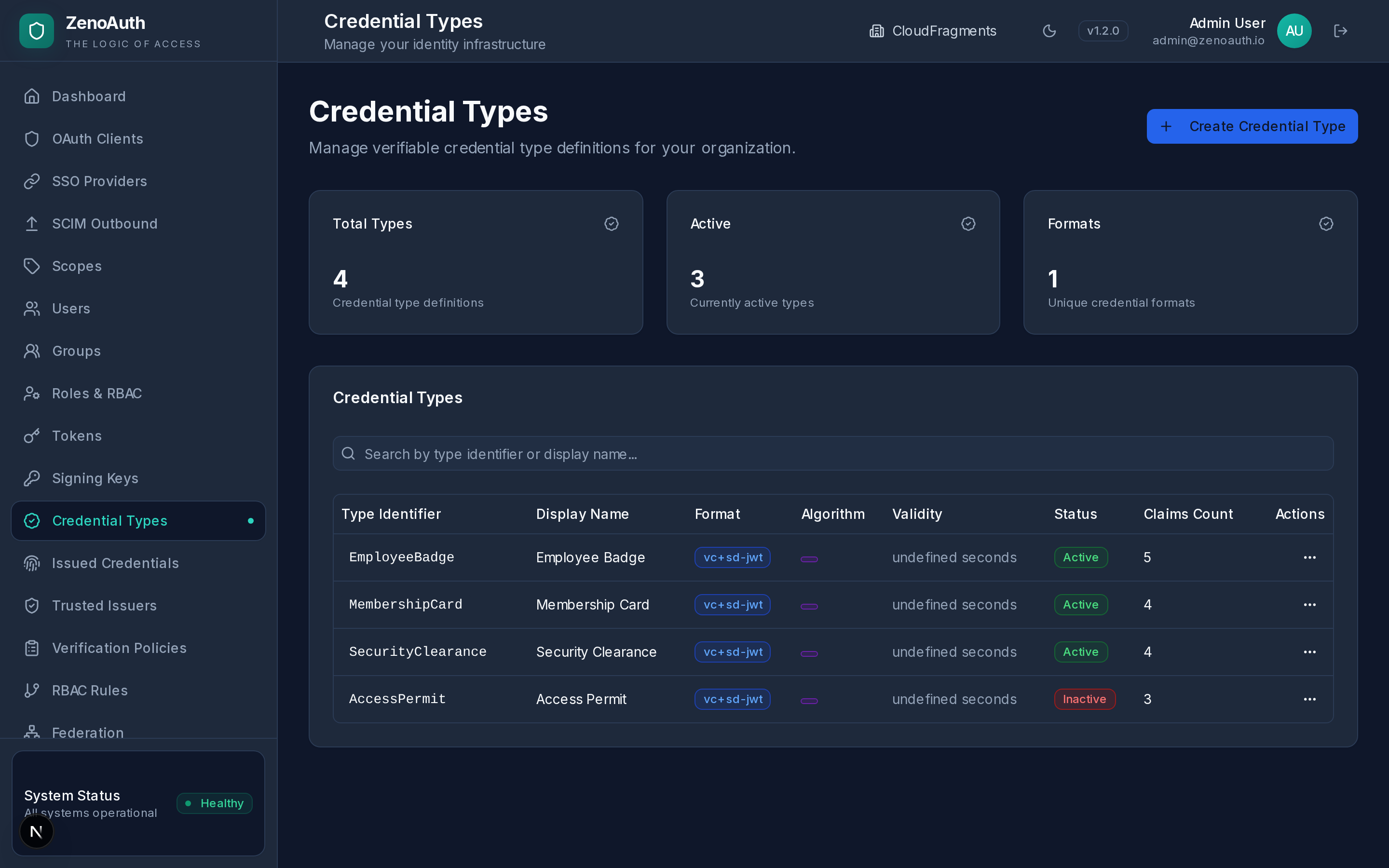
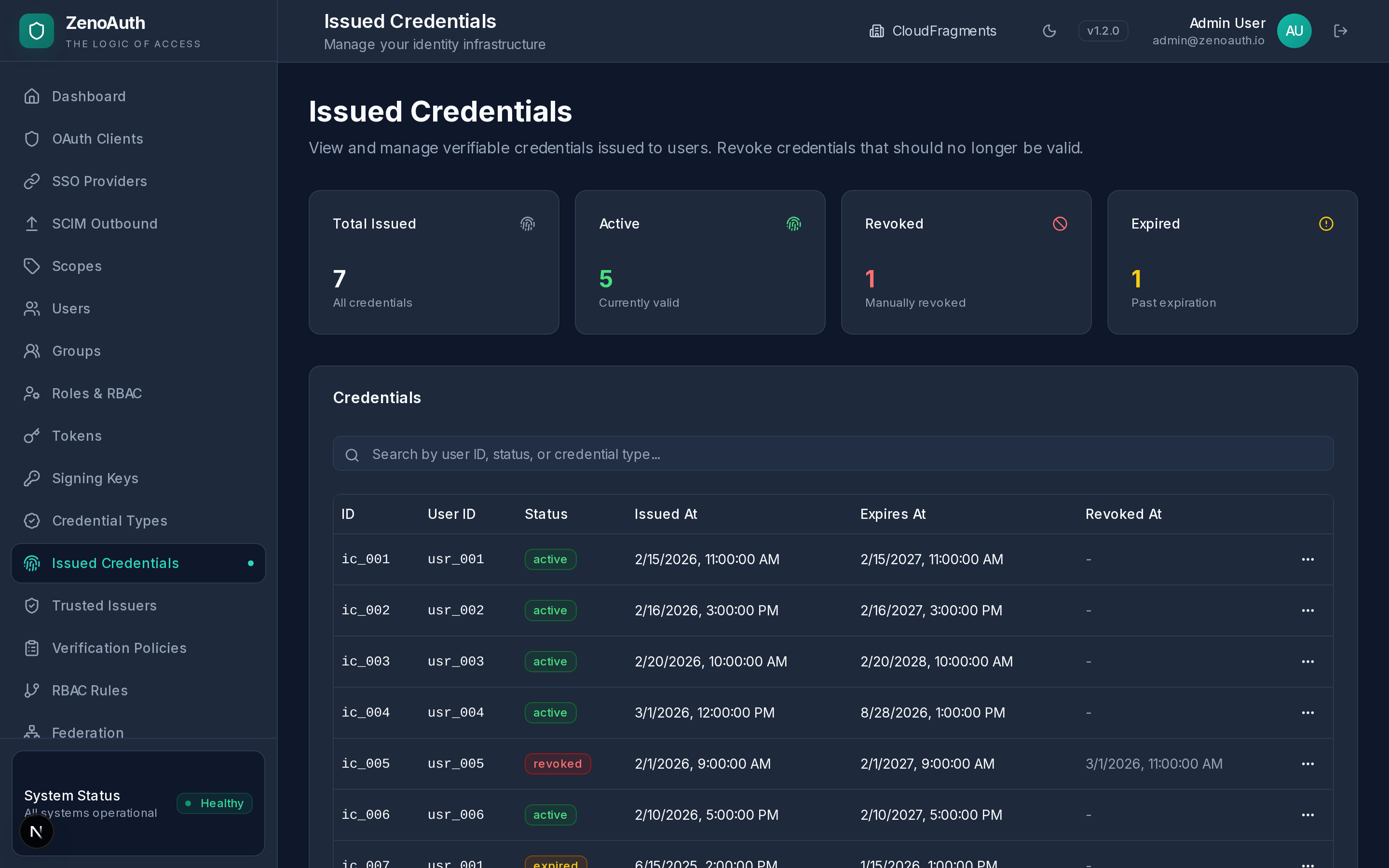
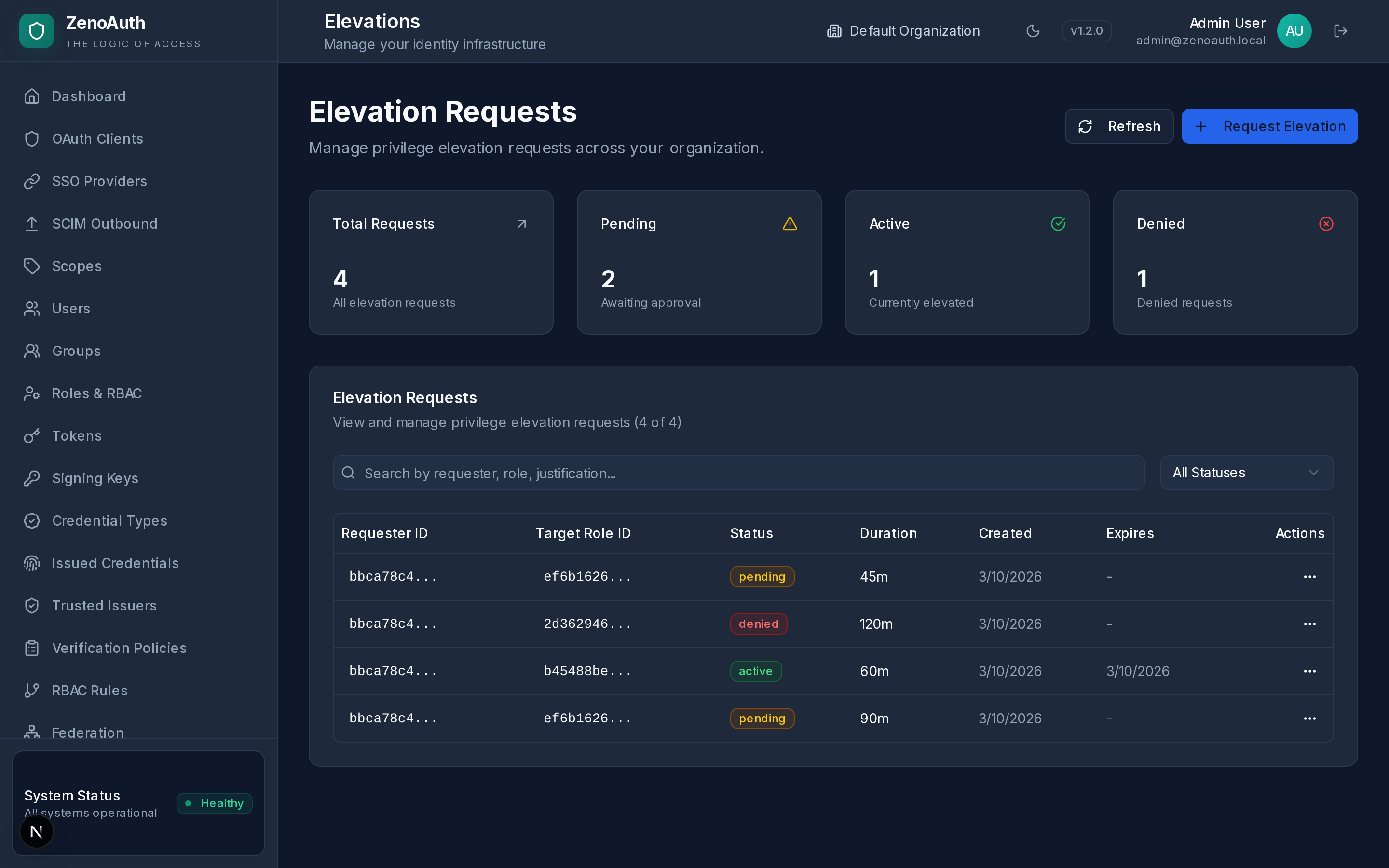
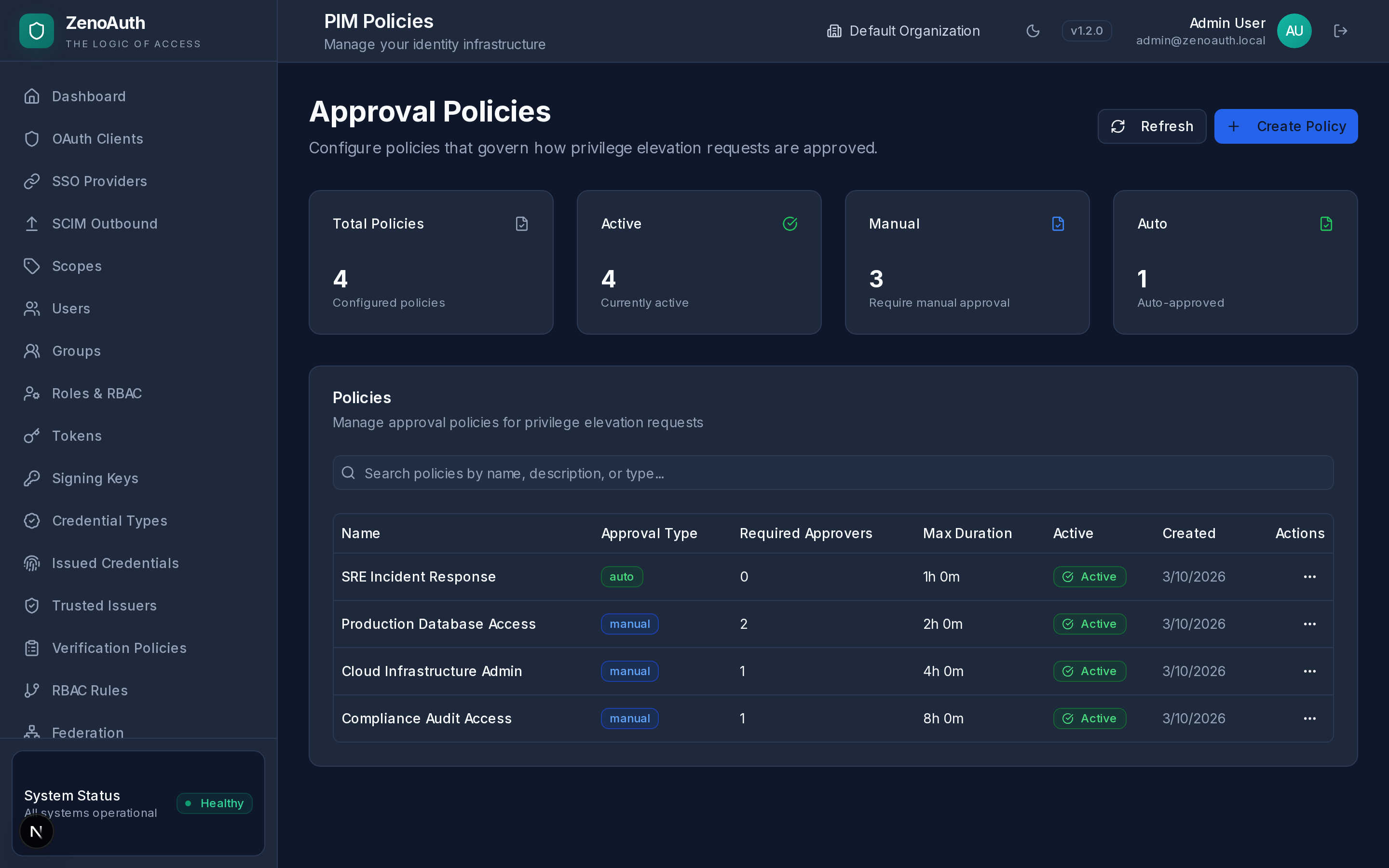
IAM + Privileged Access + Verifiable Credentials — unified.
Authentication, JIT privilege elevation, and cryptographic credentials in a single 16 MB Rust binary. One PostgreSQL database. No standing privileges. No vendor lock-in. No per-user fees for the features that matter.
Cloud from €20/month (planned 2026) · Self-hosted Contact · Unlimited users